The $3.4M 'Wrong Number' Crypto Scam That Exposed Social Engineering's Reach
CoinTelegraph reported a stunning case this week that illustrates how devastatingly simple social engineering attacks have become in the cryptocurrency space. A $3.4 million scam started with something most of us dismiss instantly: a text message claiming the sender had reached the wrong number. But this wasn't random. It was calculated. It was effective. And it was catastrophic for the victims.
The mechanics are worth understanding because they're likely to repeat.
Attackers began with a seemingly innocent message to potential targets. "Sorry, wrong number," or variations thereof. Friendly. Apologetic. Disarming. From there, the social engineering escalated gradually—seemingly organic conversations that built trust over days or weeks. Once rapport established itself, the pitch emerged: investment opportunities, often involving cryptocurrency or blockchain projects. By that point, victims felt they were dealing with acquaintances, not strangers.
That's the psychological trap.
And then it got financial. Victims were directed to send cryptocurrency to wallets they believed belonged to legitimate projects or investment funds. The wrong acknowledgement number cyber crime framework became invisible because targets never questioned the legitimacy of early interactions. The initial "wrong number" created a false sense of organic connection—no corporate coldness, no spam vibes. Just person-to-person.
The real question is: how does $3.4 million move without triggering alarm bells? The answer involves the second part of this equation: money laundering through cryptocurrency.
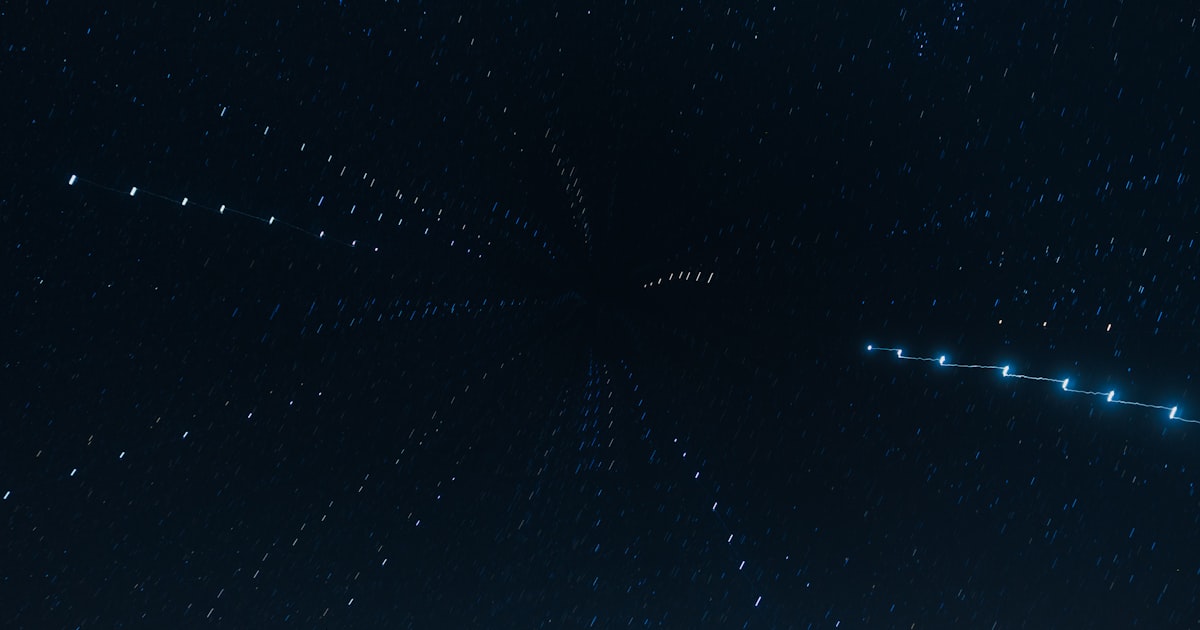
Once funds landed in attacker-controlled wallets, the funds didn't sit still. They moved through multiple crypto exchanges, cross-chain bridges, and mixing services designed to obscure transaction trails. CoinTelegraph's investigation traced portions of the haul through at least five different platforms. Law enforcement faces a nightmare here. Blockchain transactions are permanent and transparent—except when they aren't, thanks to privacy coins and deliberate layering tactics that crypto's infrastructure unfortunately permits.
So why does this matter beyond the immediate victims?
This incident illustrates a critical vulnerability in crypto adoption. Traditional banking systems have anti-fraud protocols precisely because they've suffered massive losses to social engineering. Cryptocurrencies still lack that institutional memory. There's no single gatekeeper who can flag suspicious patterns. There's no fraud department calling customers to verify $50,000 transfers. What happens when your phone number is hacked or when attackers simply buy your contact from a database remains largely your problem.
The victims' response is instructive—and depressing. Most discovered the scam weeks after sending funds, when promised returns never materialized. By then, the cryptocurrency had traveled internationally across multiple blockchains. Recovering funds became effectively impossible.
What to do if someone hacked your cell phone number is becoming an increasingly practical question for crypto holders. Best practices now require separating communication channels from financial accounts entirely. Use a dedicated phone line or email for crypto transactions. Enable two-factor authentication on everything. Screen unexpected messages aggressively. If you receive what happens to be a wrong number text from someone discussing financial opportunities, that's not coincidence—that's likely a probe.
What to do if your number is hacked should be your first concern: change passwords immediately, contact your crypto exchange's support team, and monitor blockchain activity if you've made transactions previously. The attacker likely has your contact history already.
The $3.4 million figure will spark regulatory conversations. It already has, according to CoinTelegraph's reporting. But here's what's frustrating: regulation struggles to address the root problem. You can't legislate away human psychology. You can't force exchanges to identify scam victims before they send funds. What you can do is demand better anti-fraud tooling, clearer warnings about social engineering, and genuine accountability when platforms knowingly host known scam addresses.
Until then? Trust your skepticism more than your new texting friend.